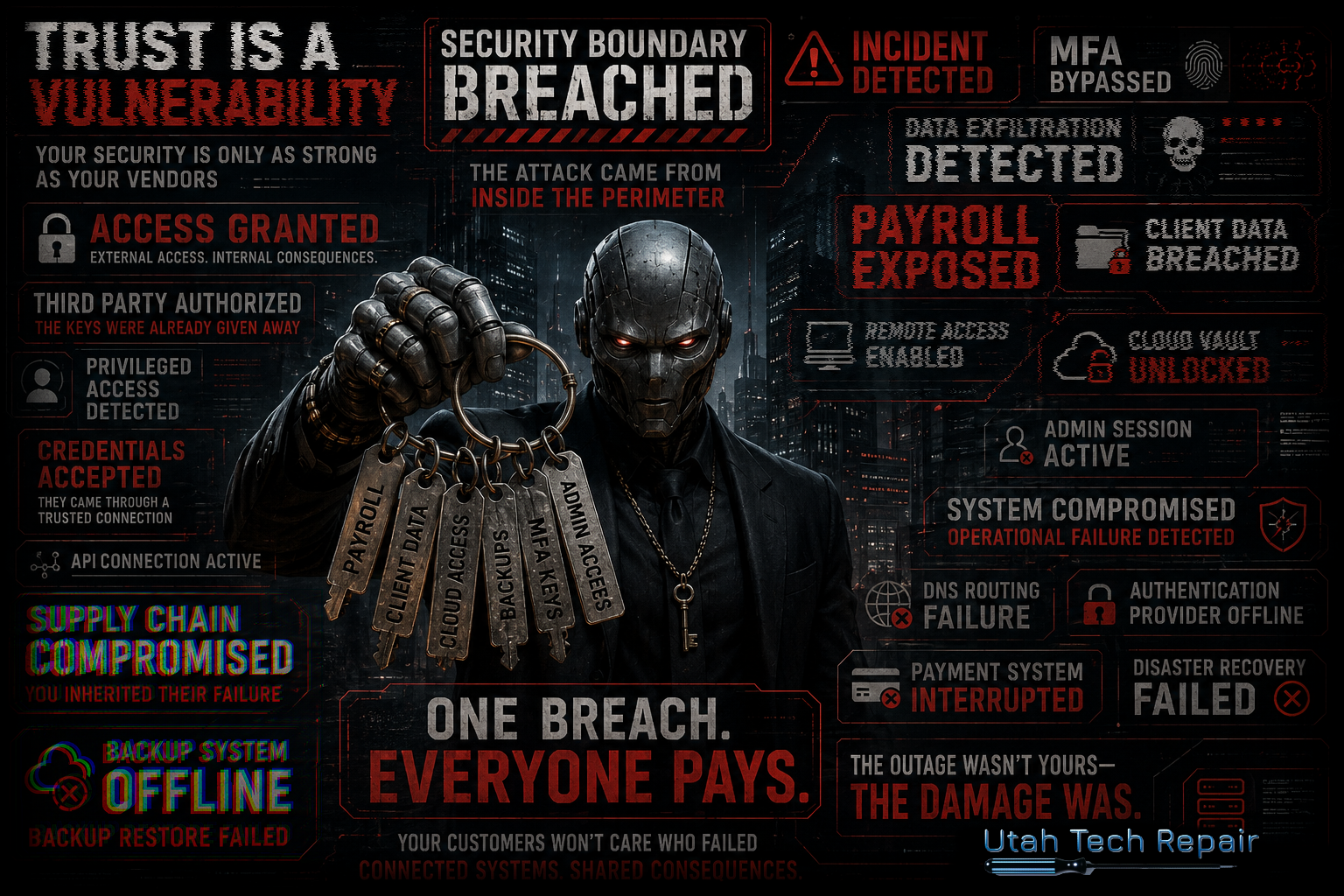
Giving A Stranger Your Keys: Understanding The Risks of Third Party Vendors
Giving A Stranger Your Keys: Understanding The Risks of Third Party Vendors
Written by: Tyson Wilcox
It’s all over the news this week. A company that is a major provider of online learning platforms for schools all across the country has been the victim of a security incident that has left their clients unable to conduct online learning and severely disrupted a key piece of their operations. The schools didn’t do anything wrong. In fact, the schools weren’t even the target, but they’re certainly the victim.
So how does an attack against a third party become such a burden on your organization? There are several risks that come to mind when talking about third party systems used within your organization:
- Impact to Operations
- Impact to Your Security Boundary
- Impact to Your Customers
Impact to Your Operations
Small and medium businesses do not have the resources to develop every required technology to run efficiently and effectively. The logical solution is to contract with vendors who specialize in the solutions that your organization needs. This is entirely acceptable and even expected. The critical thing is to remember that handing responsibility for a critical system over to a third party also means handing security responsibility for that system over to the same third party.
Let’s take a moment to talk about operational dependency. Operational dependency exists when the availability of a vendor becomes a requirement for your organization’s basic function. If the vendor goes down, your operations aren’t degraded, they’re halted.
In the recent case of the Online Classroom Provider being targeted by a cyber attack, this is exactly what happened to the schools in this case. Faculty were ready to teach, students were ready to learn, but the key software required to conduct online classes was suddenly unavailable.
This is the first hidden cost of third-party reliance: you inherit their uptime decisions.
- Their patch schedule becomes your risk window
- Their change management becomes your outage lottery
- Their incident response becomes your crisis timeline
Bottom line, you are not in control of their systems and infrastructure. You cannot deploy engineers to fix their outages or dictate their recovery priorities. You can only wait—and explain to your stakeholders why nothing is happening.
This isn’t an argument against outsourcing. Instead, this is a call for responsibility in selecting the vendors you choose to do business with. An outsourced system does not outsource the responsibility, so it is critical that companies do their due diligence to understand the policies and procedures vendors have in place to ensure uptime and disaster recovery. It simply isn’t enough to trust that they’ve taken the required steps to ensure uptime.
Impact to Your Security Boundary
We have focused heavily over the last several articles on the importance of developing your security boundary. We’ve covered the need to protect information as it flows into and out of your organization, the need to secure online accounts with unique, complex passwords backed by properly configured MFA, and the importance of protecting DNS. If your organization has been following the advice provided, then you’ve come a long way in hardening your organization’s security boundary and increasing the difficulty of criminals gaining access to your systems and information. The question you now have to ask yourself is simple: Are your third party vendors following the same strategies?
What level of access to your systems do your third party vendors have? Do they have persistent credentials or API access? Have you set up federated authentication or are they running embedded agents on your computers and servers? If the answer to any of these questions is yes, then your vendor exists inside of your security boundary. Unlike your controlled systems, however, your vendors set their own security policies, such as MFA enforcement, credential rotation requirements, and audits.
The more integrated a vendor becomes, the more your internal controls become suggestions rather than enforceable policy. Heavily integrated vendors become a part of your security posture, not outside of it.
Impact to Your Customers
Now for the hard truth - and the one that few organizations want to admit.
Your customers don’t care that the fault lies with your vendor.
The reality is that your customers trusted you to take care of their needs. They trusted that you took the required steps to protect your operations. It wasn’t their responsibility to assess your supplier risk. They didn’t approve your architecture. They didn’t sign your vendor contracts. What they did do was hand you data, time, and dependencies under the assumption that you had done all of those other things on their behalf.
When a third party fails:
- Customers experience the harm
- You inherit the explanation
- Trust bleeds regardless of where blame “belongs”
Legally, you may be able to pass responsibility off on your third party vendors, but none of that matters when your reputation - and the trust your customers place in you - has been destroyed.
The Quiet, But Predictable Pattern
None of this happens suddenly. Instead, it follows a predictable, if subtle, progression. An organization needs a solution to an operational problem. They contract with a vendor. It’s understood that there’s a risk, but all parties agree the risk is acceptable. Over time, vendor dependency deepens quietly. Failure occurs loudly when vendor systems fail and accountability becomes ambiguous.
So many organizations act surprised when this pattern plays out, but none of it is new. It is a well known and established pattern we need to stop pretending is new. The issue isn’t that third parties fail. The issue is that organizations treat trust as a feeling instead of a framework.
Taking Responsibility
None of this discussion has been intended to persuade distrust between clients and vendors. Instead, it is intended to establish the need for clarity when negotiating agreements. When making the decision to work with third parties, there are several questions that need to be asked:
- What breaks if this vendor fails?
- What access is truly required?
- What can you revoke immediately when required?
- What is outside of your control?
- If things go wrong, what responsibility will you publicly claim?
Acceptance of risk isn’t irresponsible, so long as it is done with clarity and understanding. So long as an organization understands that outsourcing functions is not the same as outsourcing responsibility.
It’s Okay To Hand Over The Keys
When you make an agreement with a third party provider, you are handing over some of the keys to your organization. Sometimes, that trade is worth the risk. But let’s be clear, once the keys are handed over, the building is still yours—and so is the responsibility for what happens inside it. That responsibility is not redirected by contracts, explanations, or press releases. Handing over the keys is sometimes required for a business to meet functional needs, and that’s okay, so long as the proper due diligence is taken in the beginning.
How Utah Tech Repair Helps
At Utah Tech Repair, we don’t believe security is about avoiding every possible failure. We believe it’s about understanding which failures you are willing to own – and which ones you should never accidentally inherit.
Our role is not to tell organizations what decisions to make, but to ensure those decisions are made with clarity. We help businesses evaluate third-party relationships, understand where vendors sit in their security boundary, and identify where operational dependency creates unacceptable exposure.
That includes:
- Reviewing vendor access and integration points
- Identifying hidden operational and security dependencies
- Helping define reasonable controls and exit strategies
- Ensuring risk acceptance is deliberate, documented, and defensible
If your organization relies on third party systems - and most do - the question isn’t whether risk exists. The question is whether that risk has been examined with the seriousness your customers and operations deserve.
If you want help ensuring the risks you take are appropriate - and the risks you avoid are intentional - Utah Tech Repair is ready to help.